A comprehensive information technology audit checklist can be a daunting endeavor.
However, the effort required to plan and execute an IT assessment is well worth it when you need to identify hazards, evaluate risks, and ensure that your IT security and disaster recovery systems are prepared to minimize downtime and protect critical data.
Click here to download our Free IT audit checklist
The IT audit process follows these four fundamental steps:
- Planning
- Defining
- Collecting
- Evaluating and Reporting
Let’s cover each one of these steps individually to give you a deeper understanding of the importance of regular IT assessments and how each step of the risk assessment process plays a role in providing the best IT services in Los Angeles for your business.
How IT Support Companies Plan an IT Audit
Although planning never really ends, it’s important to spend some dedicated time before the audit gaining a deeper understanding of how your organization operates.
First, outline the organizational structure of your business. Depending on the size of your operation, you may want to break down how each department or even each team member uses technology on a daily basis. From there, you can begin to understand the importance of each aspect of your network infrastructure.
By clarifying which system components and processes your organization depends on the most, you’re laying the groundwork to begin pinpointing and addressing risks.
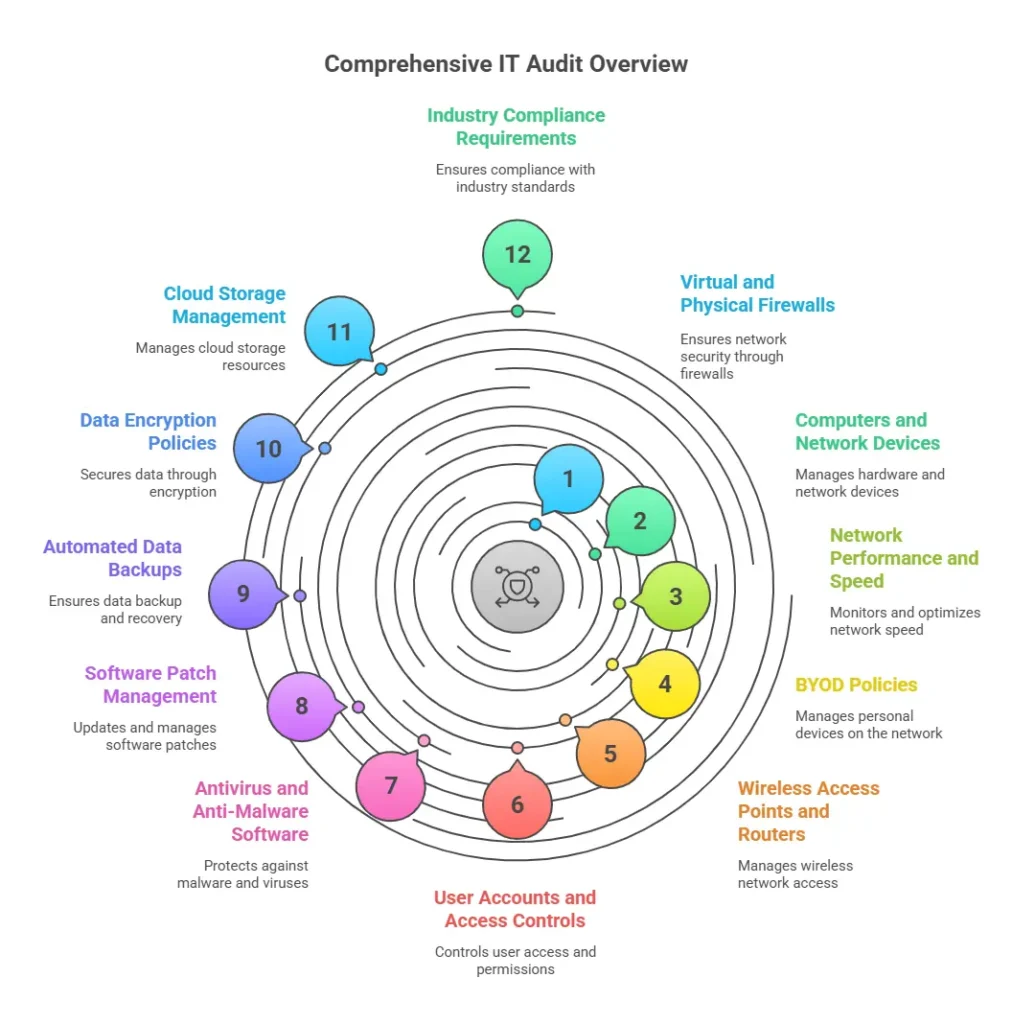
At the very least, a comprehensive IT audit should assess these critical network operations:
- Virtual and Physical Firewalls
- Computers and Network Devices
- Network Performance and Speed
- Bring Your Own Device (BYOD) Policies
- Wireless Access Points and Routers
- User Accounts and Access Controls
- Antivirus and Anti-Malware Software
- Software Patch Management
- Automated Data Backups
- Data Encryption Policies
- Cloud Storage Management
- Industry Compliance Requirements
Defining an IT Audit
Now that you have a deeper understanding of how your organization uses technology, next it’s essential to determine what the primary goal of the audit process is. Do you want to mitigate security risks, test your disaster recovery systems, or understand how you can minimize operating costs?
These are all reasonable goals to aim for when planning and executing an IT assessment. At the definition stage, you’re merely stating how your network can be improved and how that improvement aligns with your overall growth goals.
For many Southern Californian companies, some common approaches to improving your network include hiring a company specializing in Los Angeles managed IT services, but can also include :
- Reviewing control measures of your systems to ensure that they’re adequate and effective
- Evaluating system performance for servers, networks, and individual devices
- Reviewing security systems
Collecting Information During the IT Audit
Once you’ve defined what you hope to gain by performing an audit, you now need to consider how you’re going to collect concrete evidence and data relating to your overarching goal.
The three most common approaches to gathering evidence include:
Interviews
You can simply interview team members to gain qualitative and quantitative information to gain a better understanding of your systems. For example, users of an application can be interviewed to clarify how effectively they’re using security measures built into the system.
Questionnaires
Using specific questions, you can quickly gain deeper insights into how well your team understands security threats and what they’re doing to mitigate them.
Even the most basic questions are of value and there never is such a thing as a bad question. Invite all of your employees to ponder the value and security of your network. Especially now that so many employees work remotely, it’s imperative that there’s a basic understanding of how the network operates and protects sensitive information like sales data, Zoom meetings and email interactions.
Flowcharts
Flowcharts help you better understand network controls and pinpoint particular risks that are exposed by inefficient workflows.
These charts should be shared among all pertinent team members so that everyone is on the same page when it comes to how the network properly functions and what to look out for when systems aren’t running properly.
Being aware and prepared are the best defenses to possible threats and cyber attacks. If you prefer to use outsourced technical support for 24/7 network monitoring instead of handling the tasks in house, the outside team should also prepare a work flow chart so that management at least has a basic understanding of what the plan is in case of an attack.
Evaluating And Reporting After the IT Audit
Once you’ve collected an adequate amount of data for the scope of your assessment, you now need to turn that data into valuable information. Fortunately, there’s a variety of industry-specific auditing software to help you do just that.
Many software solutions also offer simplified reporting tools to ensure that your information is as valuable as possible to your organization. Once you’ve clarified system threats and weak points, your team will be empowered to address them on a proactive basis.
Although an IT audit may at first seem like more trouble than it’s worth, a managed service provider like the downtown Los Angeles IT services that Be Structured Technology Group offers can simplify every step of the process. We’re committed to helping businesses of all sizes take a proactive approach to staying protected from IT threats.
Click here to download a free IT audit checklist
Contact the Be Structured team today to learn more about how a comprehensive IT support company in Los Angeles can streamline your team’s workflows and keep you protected from tomorrow’s threats.
People Also Ask
What does an IT audit do?
A comprehensive IT audit analyzes a business’s network tech infrastructure to determine if systems are running properly and efficiently.
What is IT auditing and why do companies do it?
To make sure that the company’s tech network is running smoothly and meets compliance regulations.